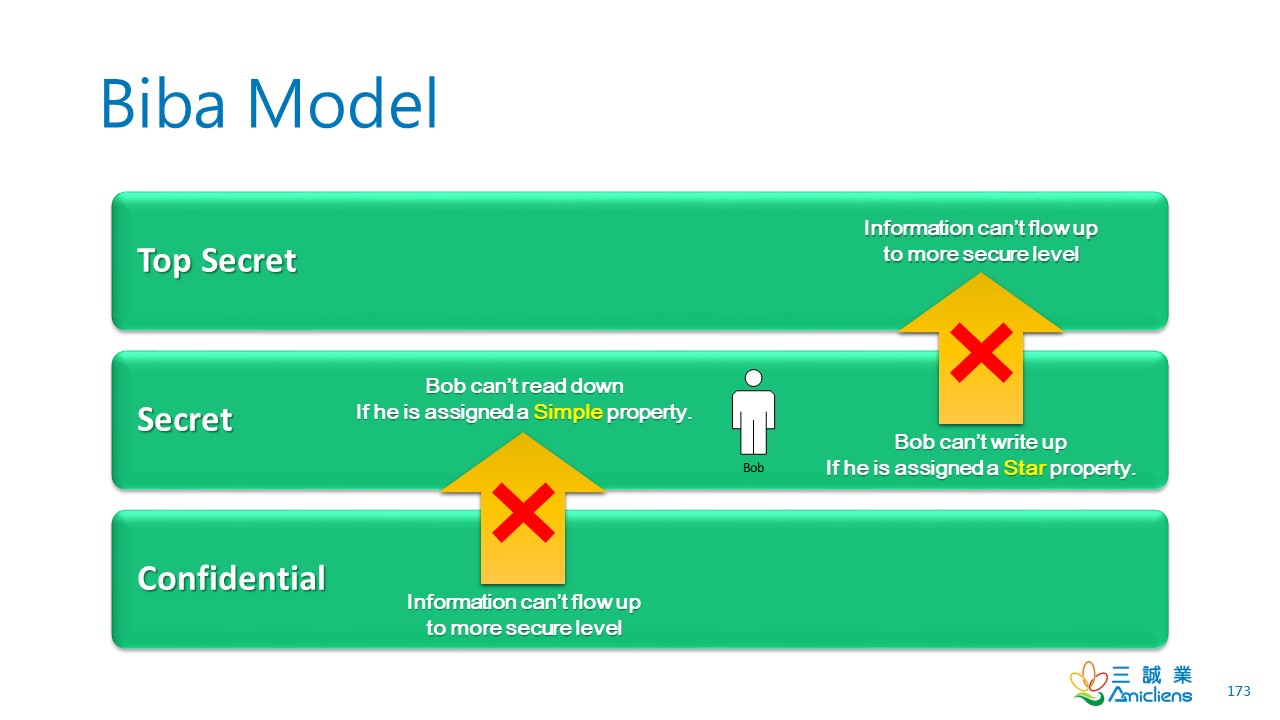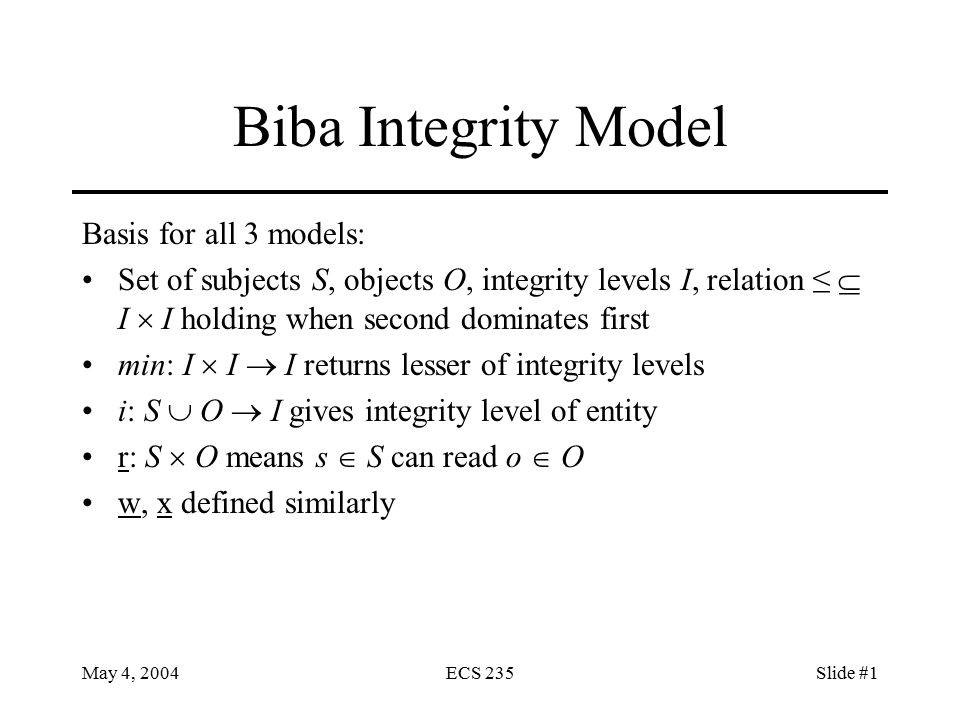
May 4, 2004ECS 235Slide #1 Biba Integrity Model Basis for all 3 models: Set of subjects S, objects O, integrity levels I, relation ≤ I I holding when. - ppt download
![PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/83fcec720b425bbc4e764ff167afaea6721dbb3e/4-Figure2-1.png)
PDF] BTG-BIBA: A Flexibility-Enhanced Biba Model Using BTG Strategies for Operating System | Semantic Scholar

Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram
Evaluation of the Appropriateness of Trust Models to specify Defensive Computer Security Architectures for Physical Protection S

Two Laws of Biba Model The satisfaction of both Biba laws, prevents the... | Download Scientific Diagram